Last Updated on July 8, 2025 by

The past few years have been turbulent, with staff turnover and the rise of remote work at an all-time high. Most companies will have noticed the impact of ‘The Great Resignation’, or will have had to make difficult redundancies in response to the pandemic and the cost-of-living crisis. With employees changing jobs more frequently, are you sure that your employee leaver process is robust enough to combat the security risks that come with IT employee offboarding?
The likelihood is, it’s probably not, which leaves your business exposed to potential cyber attacks and data breaches. In fact, research conducted by Beyond Identity found that 83% of respondents admitted to continuing to access accounts from their previous employers after leaving the company, proving that their employee IT offboarding process was not secure enough. And shockingly, 56% of respondents said they had used their continued access to harm their former employer!
So picture this, one of your employees has handed in their notice. You get busy with conducting the exit interview, collecting access cards, advertising the job, interviewing potential replacements, organising a leaving present and arranging leaving drinks for the team members. But, have you ever thought about the technical side of employee offboarding?
Neglecting to properly remove former employees from accessing your systems and applications is where the major security issues with employee offboarding lie. So next time one of your team decides to pursue another opportunity, make sure your cyber security is front of mind – did they ever really enjoy team drinks anyway?
In this article, we’ll guide you through the major security risks with employee IT offboarding and best practices for mitigating these risks. Plus we’ve compiled a quick and easy checklist you can use next time one of your staff members leave. And, discover how we can help you maximise the security of your employee IT offboarding and leaver process.
The major risks to your security when your employees leave
Whether your employee leaves the company on bad terms or not, an unreliable employee leaver process can expose you to a number of IT security and financial risks that can end up damaging your reputation.
Here are just some of the major threats that you could face without secure employee IT offboarding:
- Data breaches – if a former employee has access to company‘s confidential data, they could use this inappropriately, either by selling it maliciously on the dark web or by accidentally exposing sensitive data.
- Damage to your reputation – if disgruntled employees have access permissions to your systems, they could abuse your brand and spread malice using your company name. Think how much damage a mass email going to all clients, with harmful or inappropriate content, would cause.
- Cyber-attacks – ex-employees can sell your company data or passwords for financial gain, leaving you vulnerable to cyber-attacks from professional cyber criminals that could not only damage your reputation, but potentially bankrupt your business.
- Compliance violations – if the authorities are made aware that your employee leaver process is putting personal data at risk, you could be subject to substantial fines for breaching compliance regulations. This would, in turn, lead to financial loss, as well as the loss of public trust, and more importantly sever relationships with your clients.
The risks of an unreliable employee leaver process: A short case study
In 2018, Pagosa Springs Medical Center, a critical access hospital in Colorado, USA, found themselves at the centre of a serious HIPAA violation. And what was the route cause of the incident? A terminated employee who was not properly offboarded…
After the employee was terminated, it was found that they retained remote access to the medical centre’s calendar system, which contained the confidential medical information of at least 557 individuals.
The incident resulted in the medical centre receiving fines for $111,400 – all because they failed to properly offboard a terminated employee.
HIPAA (The US Health Insurance Portability and Accountability Act) calls out the need for a formal offboarding process under the security rule section, “Implement procedures for terminating access to electronic protected health information when the employment of a workforce member ends.”
It’s also important to note that HIPAA is just one standard that can be violated due to improper employee IT offboarding. There are many other similar regulations, not only in the US but globally, that hold similarly serious consequences for non-compliance.
Best practices for a seamless employee leaver process
So, you’ve heard how detrimental improper employee IT offboarding can be. But, how exactly do you make sure your business is secure when your employees leave?
Onboard correctly
You can do a lot to ensure smooth and frictionless offboarding processes early in the employee lifecycle — during the onboarding of a new employee. Your IT department should implement strong access control, meaning that each new employee is granted access only to the sensitive systems they need to do their job. It’s also highly recommended to use a Privileged Access Management (PAM) solution when granting permissions.
Moreover, you should set clear policies that reduce unauthorized access to SaaS services and prevent employees from storing sensitive data on insecure devices.
Communicate with HR
Cross-departmental communication is key to effective offboarding. Your HR department will be one of the first to know when an employee hands in their resignation. They’ll be able to tell you their notice period and their last day. As well as when an employee is scheduled to return from leave or if their contract is renewed.
Project management tools can help to automate the process of communicating about employee start or leave dates. But whether you have access to this or not, it’s vital that you build and maintain a good relationship with human resources specialists to ensure that all parties are clear on key dates during an employee’s tenure.
Find the right identity partner
An identity provider (IdP) is a service that stores and verifies user identity. IdPs are typically cloud-hosted services, and they often work with single sign-on (SSO) providers to authenticate users and enable them to automatically sign on to applications on their device without having to enter their credentials multiple times.
Your IdP is fundamental to the security and efficiency of your employee leaver process. Here are some things to consider when choosing an IdP:
- Ensure you can automate the deactivation of your user’s identity. This will make the employee IT offboarding process quick and efficient. You’ll simply need to set a date/time for deactivation and your IdP will do the rest.
- Enables you to immediately revoke employee’s access to all applications, devices, networks and other systems if necessary. This will allow you to act quickly if employees leave without warning.
- Has a mechanism for simple activation or reactivation so that identities can be reinstated quickly if an employee returns from leave or has their contract renewed.
Note: your IT partner will also be able to help you choose an identity provider that’s right for you!
Keep a list of technical assets
During their tenure, employees will likely acquire multiple valuable devices to be used for work purposes. It’s crucial you keep track of the technology assets they have, so that you can get them back when that employee leaves.
Types of technical assets to keep track of include, laptops, computers, iPads, smartphones, keyboard, mice, printers, headphones, USBs, routers, software licences and website domains.
Note, if you have fully remote employees who cannot easily return their technical assets, you can either arrange a reputable courier or charge these employees to keep their devices. If you do give ex-employees, you need to make sure they’re fully wiped of any company data first.
Your IT support provider should provide asset reporting for all desktops and laptops, along with recent employee login information which is a great start for the key devices you need to keep track of.
Recover and repurpose technical assets securely
So, what do you do after retrieving company assets from outgoing employees?
It’s simple! If the technical assets are still in good condition, the most cost-effective and sustainable option is to fully wipe them and repurpose them so they can be given to new employees or contractors.
Before you wipe these devices, make sure to scan them for key business data and back this up in the cloud – you don’t want to be a victim of data loss simply because you’ve accidentally deleted it!
And if you’re unsure of how to properly wipe and repurpose your technical assets, just speak to your IT partner, they’ll be able to relieve the burden and manage that process for you.
Here at Sereno IT, we use the latest NCSC approved data erasure software (Blancco), data erasure for all types of IT equipment (computers, laptops, hard drives, SSDs, servers and mobile phones etc.) allowing devices to be refurbished and reused with peace of mind knowing that your confidential data has been securely data sanitised.
Always use an employee IT offboarding checklist
There’s a lot to keep on top of when an employee leaves, we know! And if multiple employees are leaving each month, that’s a lot of admin. So, how do you keep on top of it all?
We recommend including an employee IT offboarding checklist as a key step in your employee leaver process. And to help make things easier, we’ve compiled one just for you!
Your quick checklist for offboarding your employees securely
So, here’s the employee offboarding checklist that will help you ensure a smooth IT offboarding process and mitigate legal and security threats associated with a former employee misusing their system or network access.
Track of employee exit dates
Establish a routine for your IT and HR departments to communicate clearly about employee exit dates. It will help you ensure that the company-owned devices are returned and the departing employee has no access to company systems and sensitive data.
Block account access
It is critical to have a full list of systems a departing employee has access to, such as devices, applications, customer databases, cloud systems, etc., to prevent unauthorized access. The revoking access process also involves transferring access to relevant users. In addition, make sure you block the departing employee’s remote access and terminate VPN.
Revoke email access
Your employee’s email inbox likely contains critical contacts, valuable data, and sensitive files. No one wants a former employee to have access to this data after they leave, so remember about revoking access to email on the employee’s last day.
Also, make sure that locally synched emails are wiped from a departing employee’s personal devices. Likewise, it’s important that your internal applications and Teams accounts are removed.
Update shared passwords
Sereno’s IT teams often come across a practice of employees sharing accounts. We highly discourage this practice. Still, if it’s happening at your organization, make sure your team changes the passwords in case of employee departures.
Record IT assets
As we have already mentioned, drawing up a list of IT assets and hardware linked to each employee can significantly streamline the employee offboarding process and reduce security risk.
This list should include hardware equipment (laptops, PCs, mobile devices), peripheral devices (keyboards, monitors, headphones, printers), and user accounts an employee has been using for their work (both social media and job-specific accounts).
Examine IT assets
The final item on our IT employee offboarding checklist is a careful examination of IT assets, which will help your IT department reveal damage or potential security risks. Not to mention, consider including procedures such as removing sticky keys and deep cleaning devices so that they are ready for use.
Secure employee IT offboarding with Sereno
So now you know all about what makes a secure employee leaver process, but how do you go about implementing it?
That’s where we come in… At Sereno we’re obsessed with cyber security, meaning we’re here to offer you all the help and support you need to keep your systems secure when your employees leave.
In fact, we’re here to take complete ownership of your entire employee IT offboarding process, removing 80% of the work involved with an employee leaving and meaning you don’t have to stress about disgruntled leavers or unwiped devices. As with all aspects of our IT support model, we want to take away the burden and admin of IT processes, so you can focus on your day job.
Initial IT audit & your bespoke offboarding checklist
When we first bring you onboard as a new partner, we audit your entire IT environment. This enables us to learn everything we need to know about your systems, apps, and tools. Once we have this information, we will create a thorough offboarding checklist that’s customised to the needs and set up of your business (think: an advanced and personalised version of the checklist above – that’s just for you!).
Once created, we’ll run through this with you to check that everything’s covered and you’re comfortable with our responsibilities throughout the offboarding process. This will largely involve making sure our processes are aligned with your internal processes, making sure your offboarding process is a seamless one. After this, you shouldn’t see your offboarding checklist again – because now we’re responsible for checking every box, meaning you don’t have to worry! (Unless it needs updating in the future of course – just make sure to keep us informed about internal changes).
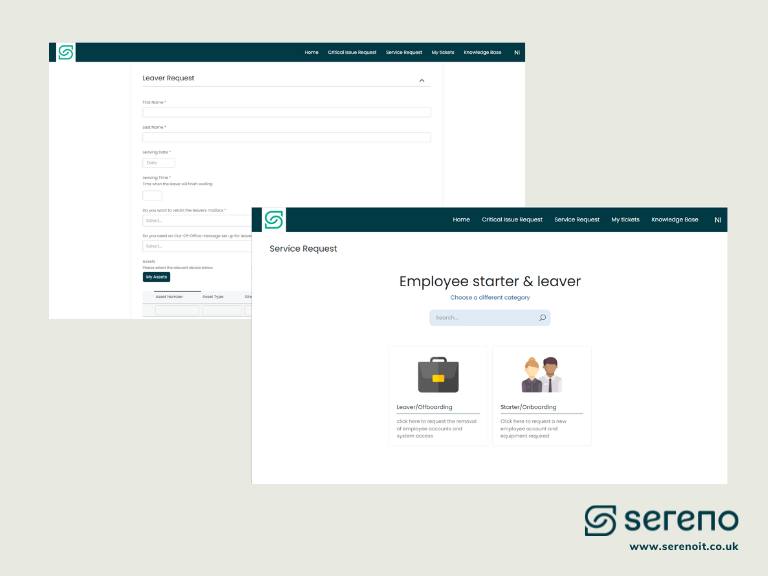
Your employee offboarding form
Now that we have all the information we need, we can create your employee offboarding form. Like your checklist, this will be bespoke to you, depending on the setup of your business. Your employee offboarding form will sit in our Partner Portal (see images below). This will include information specific to your setup and process, as well as information about individual leavers and their leaver process. For example, who’s leaving, when are they leaving, where is their mailbox being redirected to, what’s the status of their devices etc. You’ll always have access to this, so if you notice anything that needs updating you can let us know straight away and we’ll handle the rest.
Continually improving your employee IT offboarding
Whilst you’re partnered with us, we’ll continually provide recommendations based on your employee leaver process, so that you can help us to continue improving its security and efficiency.
Examples of potential improvements include:
- Restricting employee permissions based on their role, so that they only ever have access to what they need
- Fully managing your assets, so you control how your employees use their devices
- Centralised user profile management, so it’s easy to remove user access to core business systems. See the identity provider (IdP) section above.
- Same-Sign-On (SSO) so that employees have one centralised login profile, enabling them to access SaaS applications efficiently and securely, and you to easily revoke access if necessary.
- A password manager to enforce the use of secure passwords and then easily remove access to these passwords if necessary.
- Remote device wiping so that we can immediately wipe your devices whenever you need, no matter where they are.
Quick, easy and secure employee IT offboarding with Sereno
Offboarding employees effectively is crucial to maintaining security and business continuity. On each employee’s final day, you should collect and examine devices they’ve been using, revoke system access, including remote access and privileged account access, and make sure your company’s data is wiped from departing employees’ personal devices, among other offboarding steps.
The good news is that you can trust Sereno with it. Our process means that all you need to do is fill out one simple form and then hand everything over to us. Our rigorous process and trained security engineers mean that you can be sure that employees are offboarding safely and punctually, meaning your company is protected from the risks associated with employee offboarding.
To find out more about how we can help you maximise the security of your employee offboarding, or switch your IT company, please contact Sereno at 0203 089 01 41 or at hello@serenoit.co.auk to speak with one of our knowledgeable advisors on how we can help!